What is an Online Cyber Security Degree?
The focus of an online cyber security degree is to teach you about Internet threats. You will also learn how to keep data safe. You will find this field of study is also called information security (InfoSec). As an InfoSec graduate, you may leave school with key technical skills. These skills will be crucial for you to learn to detect, deter and deal with a wide range of cyber threats and security issues.
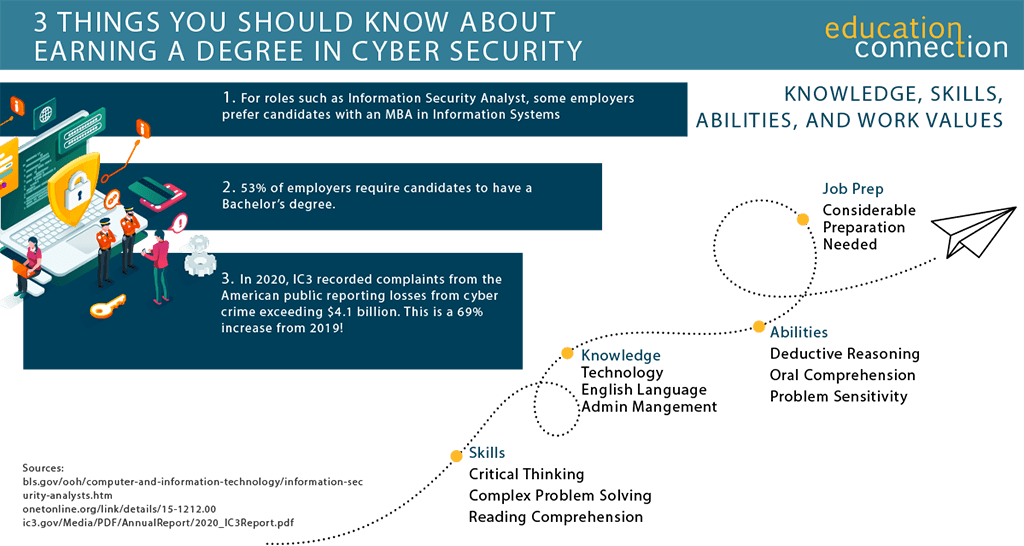
With cyber attacks real and imminent, pursuing a cyber security degree online may be a worthwhile venture for you. You can see in the reports that by 2022, there will be 3.5 million open cyber security jobs. Thus, you are wise to be prepared to meet this alarming trend by studying InfoSec. Your trained eye and computer savvy skill set will be in demand to employers.
TYPES OF ONLINE CYBER SECURITY DEGREE PROGRAMS
Associate of Science in Cyber Security
In this program, you may cover basic concepts, products and practices. As a student, you could train in computer networks through courses in security defense tactics and strategy.
Course Examples
- Dynamic Network Defense
- Security and Vulnerability Tests
- Digital Forensics
BS in Cyber Security
In addition to covering basic concepts, and practices, you may learn how to apply current tools. You could also test out methods, and, in addition, you could learn how to design secure systems. An optional internship may give you even more hands on experience.
Course Examples
- Ethical hacking
- Network Security
- Digital Forensics Malware Reverse
MS in Cyber Security
As a student, you may be exposed to to the latest tools, practices, methods and procedures used to manage and protect critical information infrastructures. You could also study other sensitive assets. In this program, you may learn to investigate current trends and emerging threats in the industry.
Course Examples
- Cyber Security and Policy
- Terrorism and Organized Crime
- Security Risk Management
Online Cyber Security Degree Levels
As an undergrad enrolled in an online cyber security program, you will learn the basics of cyber crime. At first, you may study what it means for you to be the on the first line of defense against cyber attacks. Further on, you may also fine tune your interests by focusing on another aspect of cyber security that interests you.
In some programs, you could look at trending issues in network safety. You could also cover identity theft, computer viruses, and hacking. In addition, you may study cyber terrorism and homeland security (HS).
The courses you take may teach you to see a clear picture of what intruders look like, and how you can guard against them. Learning these skills will be vital to you when it comes to protecting your organization’s digital assets.
You may also learn things such as which tactics and protocols to use. Just like students enrolled in software development programs, you may find that many courses are technical and computer focused. As such, you could also learn how to use software tools to keep information systems safe from intrusion.
If you take other courses in digital forensics, they may help you to develop your investigative skills, as well. These skills are crucial for you when it comes to solving security related problems.
1
Southern New Hampshire University
- Take advantage of some of the nation’s most affordable tuition rates, while earning a degree from a private, nonprofit, NEASC accredited university
- Qualified students with 2.5 GPA and up may receive up to $20K in grants & scholarships
- Multiple term start dates throughout the year. 24/7 online classroom access.
Popular Programs
Business Administration, Psychology, Information Technology, Human Services…
2
University of Arizona Global Campus
- 99% of University of Arizona Global Campus students study online
- University of Arizona Global Campus offers affordable tuition, so college is accessible to many students.
- he University of Arizona Global Campus (formerly Ashford University) is accredited by WASC Senior College and University Commission (WSCUC)
Available Programs
Accounting and Finance, Information Technology, Political Science…
3
Western Governors University
- Award-winning programs created to help you succeed.
- A quality education doesn’t have to be expensive. Earn an accredited degree for less.
- Programs start monthly – Apply free this week!
Sponsored Schools
What Courses Will You Take In An Online Cyber Security Degree?
One of the things you can expect to study is how someone hacked a system. As such, by tracing his or her steps, you will learn about taking risks. In so doing, you will learn how you can fix vulnerable and weak systems. Your program may cover counter measures, and also teach you to master various industry tools.
To round out your course of study, you may need to take some general education courses and a capstone. You may expect to cover topics such as math, computing and information technology. Core course samples you could take may include:
Ethical Hacking: Learn the advanced hacking tools used to break into an organization in a lawful and legitimate way.
Network Defense: In this course, learn concepts used in defending a network, and techniques that can be used to protect a network from cyber threats.
Cyber Security Policy: In this course, you could learn about how to help organizations protect their data, identify and manage cyber risk, and recover from cyber attacks.
Database Basics: Learn the basics of creating tables and selecting data in various different ways. You could learn structured query language (SQL) as well.
Digital Forensics: In this course you could cover the investigation of computer related crimes. Learn how to obtain evidence to present in a court of law.
Security Risk Management: In this course, you could gain comprehensive knowledge of risk management and the theories, concepts, and best practices.
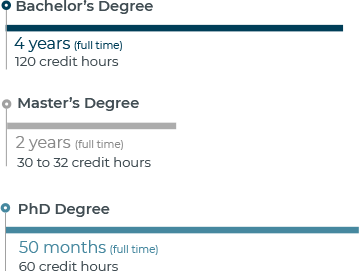
HOW LONG DOES IT TAKE TO EARN A DEGREE IN CYBER SECURITY?
If you study full time, it may take you four years to earn a degree in cyber security. You could expect to spend two years on a master’s degree.
That said, many schools will offer you ways for to graduate sooner. An accelerated program is one route you could take. This would allow you to transfer your credits. Let’s say you have an associate’s or BA degree from an accredited school. You may then apply these credits to achieve a shorter timeline. You could expect the same at schools that offer you credit for military training.
ONLINE CYBER SECURITY DEGREE PROGRAM EXAMPLES
| School | Degree level | # of Credits Required | Start Dates | Minimum Months to Complete |
|---|---|---|---|---|
| Rasmussen College | Associate | 90 credits | Multiple | 18 months |
| Purdue University Global | BA | 180 credits | Multiple | You may apply up to 75% of undergraduate credits to graduate faster |
| Colorado State University Global Campus | BA | 120 credits | Every 4 weeks | You may transfer up to 90 credits to graduate faster |
HOW MUCH DOES IT COST TO GET AN ONLINE CYBER SECURITY DEGREE?
On average, you could expect to pay $28,890 and up to earn your online cyber security degree. That said, your costs could depend on a few things.
One thing you should know, which could impact your costs, is state residency. Some schools charge more if you are an out of state student. Others, however, may charge you a set tuition. In other words, you would pay the same as all online students. You can see that current data shows a median in state tuition of $6,826 (growing 3.89%). The avg out of state tuition ($28,890) is also growing (by 5.16%). You may also have to pay extra for your technology fees.
| School | Degree Level | # of Credits Required | Cost Per Credit | Total Tuition Cost |
|---|---|---|---|---|
| Purdue University Global | BA | 180 | $371 | $66,780 |
| Regent University | BA | 120 | $395 | $47,400 |
| Colorado Technical | BA | 182 | $325 | $59,150 |
TOP CYBER SECURITY DEGREE PROGRAMS
At last check, you can see that most schools that offer cyber security programs are public. Many are also two year institutions. Out of those schools, you’ll find there were 11,906 degrees awarded to students.
| School | 2021 Grads total/Degrees awarded | 2023/24 Tuition (Out of State unless *) |
|---|---|---|
| University of Maryland-College Park | 1339 | $40,306 |
| Western Governors University | 830 | $8,300* |
| University of Phoenix Arizona | 566 | $9,552* |
| American Public University System | 352 | $8,400* |
| ECPI University | 336 | $18,484* |
| Pennsylvania State University Main Campus | 232 | $40,188 |
| Anne Arundel Community College | 231 | $11,330 |
ACCREDITATION FOR ONLINE CYBER SECURITY DEGREE PROGRAMS
It is to your benefit that you look for an accredited online cyber security program. For one, regionally accredited schools may allow you to transfer credits. And, any time you can apply past credits, you will have less work to do. You will also have less to pay for. In addition, you could apply for federal financial aid.
The next level you could pursue is professional accreditation. This kind of approval speaks to what the school will teach you. It will assess whether the courses you take meet industry standards.
Because this process is voluntary, you will see that the school must submit an application. First, it must pass the approval of peers and meet criteria. Then, it will earn the status “accredited.” Recently, you will see, the ABET began to approve cyber security BA programs.
Not as new, is the designation as a National Center of Academic Excellence in Cyber Defense (NCAE CD).
The National Security Agency (NSA) and the Department of Homeland Security (DHS) jointly sponsor the NCAE CD program.
You will find that the goal of such programs is to teach you cyber defense expertise. On the NSA website, you can check to see if a two year, four year or graduate school is CAE CD approved.